Fraud scams continue to go from strength to strength, particularly as we see the spike in FluBot scams spreading across the world. In 2021, the UK reported more than 1.2 million domains linked with the Android malware FluBot that was distributed to the public via ‘missed delivery’ scams. The pandemic also created new hooks for fraudsters to snare victims by impersonating vaccine rollout and vaccine passport information.
FluBots are lucrative for scammers because they act as both a banker and spyware. So, when an unsuspecting victim clicks on the link, they accidentally download malware to their smartphones that will steal the user’s credit card or bank information. It will then copy the user’s contact list and automatically send the infected links, via SMS, to all of the user’s friends and family.
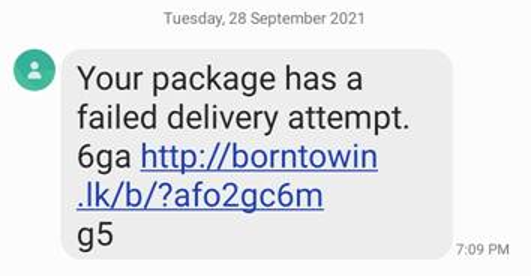
FluBots are hard to stop in their tracks because they are often launched as rolling campaigns where the malware remains the same, but the message used to carry it and the domain hosts are constantly changing. This means that traditional rule-based methods of identifying malicious attacks through keyword searches alone will not suffice. Because of this, CSPs should ensure that their SMS security addresses the challenges of both today and tomorrow.
SMS Security Checklist
- AI and ML-based protection: enables the continuous learning and discovery of unknown threat patterns for quicker protection
- Reduces Spam – stops large amounts of unwanted messages from reaching subscribers
- Prevents Wangiri SMS Fraud – stops fraudulent attacks sent through malicious links
- Protects against viruses – stops messages with binary common content
- Eliminates SMS fraud – prevents SMS messages from unauthorized sources
- Controls traffic from grey routes: reduces revenue leakage by using machine learning models along with multiple coordinated policies that work together to detect and block unwanted messages and reduce revenue leakage by controlling traffic from grey routes.
- Multi-faceted content analysis: to complement ML detection, additional SMS content analysis should be performed to detect the presence of URLs, Phone Numbers, e-mail IDs, and other keywords within the messages.
- Supports international, domestic, and on-net traffic: Ensure the SMS Firewall protects against SMS spam and A2P messages sent over SS7 signaling networks, including international, domestic, and on-net traffic.
- Provides Integrated Fraud and Security Protection: Make sure to check that the solution also detects the misuse of the short message peer-to-peer protocol (SMPP) and provides critical analytics functions that protect against security and fraud threats.
- Compliant to industry-leading standards: such as FS12 A2P SMS bypass, SG22 SMS Firewall best practices, IR71 SMS Fraud, FS.11 SS.7 signalling, FS.19 Diameter Signalling, FS.20 GTP signalling.
Mobileum’s SMS Firewall was recently recognized as a market leader by Juniper Research as the Gold winner for Best SMS Firewall. At the Awards, Mobileum’s SMS Firewall solution was recognized for its ability to protect both SMS revenues and subscribers from fraud. The solution uses AI and machine learning-based algorithms to discover unknown threat patterns and block unwanted messages, preventing SPAM and malicious Smishing attacks from reaching subscribers. In addition, Mobileum’s SMS Firewall reduces revenue leakage by controlling A2P grey route traffic and blocking non-commercialized traffic where there are no agreements between sending and receiving networks. While point solutions deliver partial protection, leaving consumers and networks at risk, when combined with Mobileum’s Fraud Management Solution, Mobileum’s SMS Firewall can protect an operator’s subscriber base against several types of threats, including Wangiri fraud, by performing contextual analyses between security and fraud management feeds.
Contact us today to eliminate the threat of smishing, FluBot, SMS interception, SMS bypass, SIM Boxes, and SMS spam while assuring your A2P SMS revenues.







Give us your comments
Let us know what you thought about this article